Casper vs Avalanche
Within this article, we shall do a mini deep dive into the Avalanche layer 1 blockchain, specifically the Avalanche snowball consensus protocol and conclude with comparisons to the Casper layer 1 blockchain and CBC consensus protocol and finally argue why we believe CSPR is the stronger of the two tokens.
As we have extensively covered CSPR in our previous articles, we shall focus on first providing insights into AVAX and the snowball consensus protocol before moving to the comparison and concluding with a summary. We recommend first reading our deep-dive of the CSPR token here.
Avalanche Overview
Avalanche (AVAX) was founded in 2018 and launched via an ICO in July 2020. AVAX is advertised as the foundations to create and trade digital assets globally, in a legally compliant way. The aim of the project is therefore to create a single market place (unified global network) where previously fragmented markets (due to regulatory and geographical differences) such as equities, commodities and alternative can be deployed and traded.
AVAX is built on the Avalanche snowball consensus protocol. This consists of multiple subnets that form a heterogeneous interoperable network of many blockchains. Anyone is free to create a tailor-made application specific blockchain (subnet) which supports custom virtual machines. Each subnet consists of a dynamic set of validators working to achieve consensus.
An asset provider can launch an asset on the network by setting the following:
- The features of the asset
- Whether it wants to be on a permissioned or permissionless platform
- Customizable smart contracts
- Conditions to meet regulatory needs
Avalanche Consensus Protocol
The Avalanche ‘Snowball’ consensus protocol uses a process similar to the central limit theory statistical method to arrive at a consensus. For those unaware, central limit theory is a simple process which allows to find the average of a population without having to know the detail of every item in the population:
Central Limit Theorem: Imagine there are 1000 students and you wanted to obtain the average height. You can either (1) take the height of every student and then divide by the number of students, or (2) you can take a sample of 30 students, obtain the average and the repeat by taking several additional samples and calculating the average of each sample, You can then approximate the average height of the population by calculating the average of the sample averages.
The specific method which the Avalanche protocol uses is the following modification to the above.
- Firstly each node will have a view of the state (eg shall I get pizza or pasta for lunch…I choose PIZZA, my view)
- Each node then will check the view of the state from ‘k’ additional nodes (where ‘k’ is a subset of other validators. i.e. NOT every other validator – For example if there are a total of 1000 nodes, they might check with 30). There are then 3 possible outcomes:
- If more than α (quorum size, an arbitrary variable parameter which indicates a number of validators you need to have in agreement which is less than the sample size ‘k’) agree on a state value and the value agreed upon is the same as the original node (i.e. PIZZA), then the original node will keep its view of the state the same (PIZZA) and a counter called ‘consecutiveSuccesses‘ is incremented by 1. The sample test is run again with another sample of different validators.
- If more than α (quorum size) agree on a state value and the value agreed upon is the different to the original node (i.e. PASTA), then the original node will change its view of the state (from PIZZA to PASTA) and will then run another sample. the consecutiveSuccesses counter is reset to 1, The sample test is run again with another sample of different validators.
- If less than α (quorum size) can agree on a state then the sample test is invalid and the sample of validators do not have enough in agreement. The consecutiveSuccesses counter is reset to 0.
- The sampling is repeated over and over until the number of consecutiveSuccesses reached a parameterized threshold β.
Avalanche Consensus Protocol – Coded
You can note the detail in the below block of code:
n: number of participants
k (sample size): between 1 and n
α (quorum size): between 1 and k
β (decision threshold): >= 1
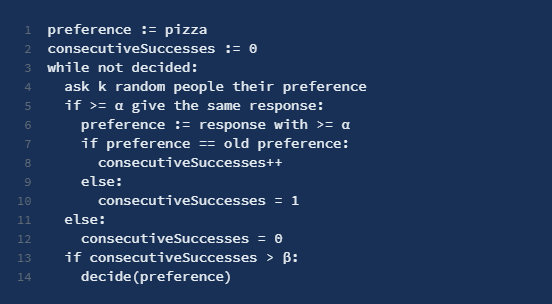
The way to interpret the consensus protocol is that unlike many other consensus protocols:
- The protocol uses a statistical method.
- The statistical method is run by each validator. i.e. there is no process outside of the validators which samples the validators. If the method was run in a layer 2, i.e. sampling the validators in a central limit ‘mean of means’ way by a process outside of the validators, they would not need to be able to change the state of each validator, as they are currently doing. However this process will suffer from performance issues with an increase in the number of validators.
- However as each validator is running the statistical method, to make this work they have had to ensure that a validator is able to change their view on the state dependent on the outcome of the test. This is an extremely important aspect of the protocol. It is this aspect which means that AVAX can sustain a very large number of validators….but it has its drawbacks….
DAGs (Directed Acyclic Graphs)
The protocol’s implementation will fail without partial ordering of decisions, due to its iterative nature. Directed Acyclic Graphs (DAGs) will enable this partial ordering. Unlike linear blockchains where every block has one parent and one child, Avalanche uses a more lattice based approach with ancestors and descendants (potentially multiple of each). The lattice uses two properties:
- Chit – If a node gets an α majority response for a transaction then you give that transaction a chit
- Confidence – sum of a vertex’s chit plus the sum of its descendants’ chits
Using a concept of vertices, optimizes throughput. These are similar to blocks in a linear blockchain, allowing batching and voting in groups of transactions. If a node receives a vote for a vertex, it counts as a vote for all the transactions in the vertex. A Vertex is accepted when all the transactions contained in it are accepted. The rejection of a single transaction will result in the rejection of the entire vertex.
Validators
Validator need to stake physical AVAX in order to gain influence on the network, as is the case with any Proof-Of-Stake network, The more AVAX a node bonds, the more often that node is queried by other nodes. Due to the nature of the snowball consensus above, it is irrelevant of the number of validators on the network grows to an extremely large number as the consensus is based upon subsampling. With Avalanche each validator in a subnet is responsible for validating the transaction in their subnet, but also on the main chain
Comparison with CSPR
We shall now focus on drawing some comparisons of AVAX with CSPR
- Network nodes:
- Avalanche makes it very easy to run a node. On their home page there are instructions on how to run a node (1) from a home computer (2) from AWS and (3) from Azure. The node running from home uses VirtualBox to setup a partition on your home PC to install Ubuntu. The minimum requirements for an Avalanche node is 16GB RAM.
- CSPR at present has 100 validators which are able to run on standard servers as the node only required 32 GB of RAM.
- The key differences here is that AVAX is promoting running a node from home (with the increased downtime risks due to power or network connectivity issues), whereas CSPR is promoting the use of stable bare metal servers for their nodes. So why is this? The CSPR network wants to ensure that nodes have the maximum possible uptime due to the fact the consensus protocol is reliant on the view from all validators whereas with AVAX, the strategy is to grow the physical number of validators to as large as possible as the snowball consensus relies on a more statistical means for validating transactions. Which is better? The answer lays with which consensus protocol is safer (discussed in the security section below).
- Decentralization:
- AVAX will have over time, significantly more validator nodes than CSPR, due to the ease in joining the network.
- The risks with the AVAX model however lays with the subnets. We have learnt from above that it is possible to launch a subnet (bespoke blockchain) within the Avalanche infrastructure. The goal of the project is to have an interplay between various subnets. The problem arises however when we consider the validator nodes within each subnet. This population will be considerably smaller than the global population of nodes on the primary network as we know that all subnet validators are also required to approve transactions on the primary network.
- With the above – we can consider a simple scenario where there are 10 subnets running on the primary network. Each subnet having 50 validators. Now when considering the primary network, we would see 500 validators, however each subnet is only using 50 and therefore the network as a whole should not be considered as decentralized as the total node count implies. This will also have quite severe and asymmetric risks across the network. Discussed in a section below.
- CSPR is currently running 100 validator nodes across its network, with an option to increase this if needed.
- Throughput:
- This is an interesting comparison. We know that in using the snowball algorithm, Avalanche can achieve over 4500 transactions per second and also boasts impressive finality (as acceptance / rejection of blocks are final).
- This compares with CSPR which is currently achieving 2.5k transactions per block (100 WASM deploys per block)
- The key to understanding this difference is in understanding how the snowball algorithm works and what is being compromised to gain this increased throughput. Discussed in the ‘security’ section below
- Security:
- The security and finality of the CSPR network has been covered in these two articles: CBC and Highway. From the articles its clear that CSPR is a powerful non-statistical method to guarantee security and finality given a threshold of malicious nodes.
- For AVAX, the network us built across parameters which can be customized (n:, k, α, β). This means that for AVAX, security is in fact optimal and not guaranteed. Lets look into this a little further:
- With the parametrization in the Avalanche paper, specifically with alpha=0.8, Snowball can stall (loosely defined as still being in the state of unstable equilibrium after 500 iterations) with just 17% malicious actors. And the only action that the malicious actors need is to split into two equal groups and always respond with the same state within each group. With lower alpha’s the percentage is higher, but the number of steps to converge in normal circumstances also grows rapidly. Read the full critique here.
- We have already touched upon the issue where a subnet is only as secure as the number of validators in the subnet. The implications of this are that this results in materially different levels of security across the chains within the system. Inter-shard attacks become feasible, as messages from one (less secure subnet) may be able to effect a transition on another (more secure) subnet. In effect, the entire system becomes only as secure as the least secure subnet.
- Slashing:
- Both CSPR and AVAX do not impose any fine for maliciously nodes.
- CSPR implements jail time.
- Enterprise adoption:
- Both CSPR and AVAX offer private chains.
- The focus from AVAX seems to be very specific and niche to the field of asset trading, whereas CSPR is targeting a more general market.
- Future Proof:
- The design and engineering of CSPR ensures it is a fully future proof blockchain. It has achieved this by ensuring all components (Execution Engine, Network Engine, Consensus Layer) are pluggable. This allowed the blockchain to be upgraded with relative ease. In comparison, AVAX has taken the stance to implement a statistic method within its consensus protocol meaning that it can scale in size, however to the detriment of security.
Conclusion
The key to the performance achieved within AVAX lies within the statistical approach taken in their consensus protocol. As with any statistical approach, you are assuming the properties of a sample reflect those of the population distribution. This inherently applies a degree of approximation as the assertion may not be correct. In trying to address this, by allowing a node to flip its state via the snowball avalanche approach, the blockchain seems to have caused additional issues. This coupled with the subnet approach bares a degree of risk to the system. Mass adoption and a large number of validators could mitigate this risk.
On the contrary, the approach CSPR has taken is to firstly ensure maximum possible security on the network before then looking to tackle performance issues such as throughput. They aim to do with with an innovative sharding solution which you can read about in more detail here.
Both blockchains are targeting the public and private market, looking to promote enterprise adoption as well as public side dapp development, With regard to the comparison of nodes, its very interesting to find that AVAX are encouraging Virtualbox Ubuntu nodes on home PCs, this further adds weight to our view that a substantial number of nodes are required to improve the security on the network.
Disclaimer: This article is for the purposes of research and does not constitute financial advice or a recommendation to buy.